Improved BlackCat Ransomware Strikes with Lightning Speed and Stealthy Tactics
The threat actors behind BlackCat ransomware have come up with an improved variant that prioritizes speed and stealth in an attempt to bypass security guardrails and achieve their goals.
The new version, dubbed Sphynx and announced in February 2023, packs a "number of updated capabilities that strengthen the group's efforts to evade detection," IBM Security X-Force said in a new analysis.
The "product" update was first highlighted by vx-underground in April 2023. Trend Micro, last month, detailed a Linux version of Sphynx that's "focused primarily on its encryption routine."
BlackCat, also called ALPHV and Noberus, is the first Rust-language-based ransomware strain spotted in the wild. Active since November 2021, it has emerged as a formidable ransomware actor, victimizing more than 350 targets as of May 2023.
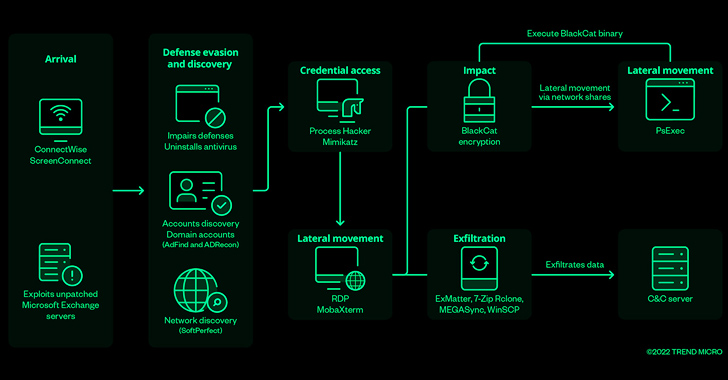
The group, like other ransomware-as-a-service (RaaS) offerings, is known to operate a double extortion scheme, deploying custom data exfiltration tools like ExMatter to siphon sensitive data prior to encryption.
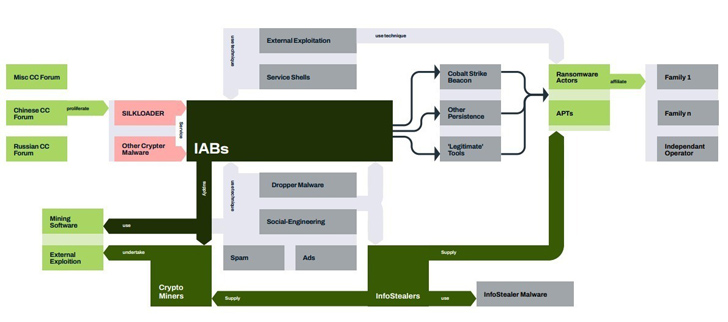
Initial access to targeted networks is typically obtained through a network of actors called initial access brokers (IABs), who employ off-the-shelf information stealer malware to harvest legitimate credentials.
BlackCat has also been observed to share overlaps with the now-defunct BlackMatter ransomware family, according to Cisco Talos and Kaspersky.
The latest findings provide a window into the ever-evolving cybercrime ecosystem wherein threat actors enhance their tooling and tradecraft to increase the likelihood of a successful compromise, not to mention thwart detection and evade analysis.
Specifically, the Sphynx version of BlackCat incorporates junk code and encrypted strings, while also reworking the command line arguments passed to the binary.
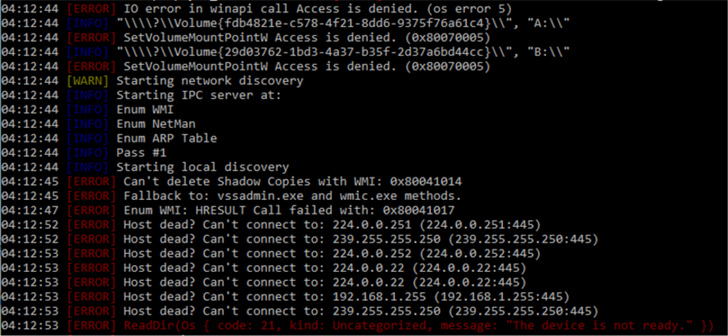
Sphynx also incorporates a loader to decrypt the ransomware payload that, upon execution, performs network discovery activities to hunt for additional systems, deletes volume shadow copies, encrypts files, and finally drops the ransom note.
Despite law enforcement campaigns against cybercrime and ransomware groups, the continuous shift in tactics is proof that BlackCat remains an active threat to organizations and has "no signs of winding down."
Reference link
A.K



Comments
Post a Comment